🔐 Password Manager Extension
An extension for MIT App Inventor 2.A powerful Java-side password system for your Kodular apps!
 What is it?
What is it?
Password Manager is a professional-grade Kodular extension that helps you securely manage passwords inside your app — no extra component required!
Keep your users’ credentials safe with industry-standard one-way hashing.
No AES, no reversible encryption — just strong, secure, and irreversible protection.
 Features at a Glance
Features at a Glance
 Strong Security by Default
Strong Security by Default
Uses PBKDF2WithHmacSHA256 with salt + iterations (200k by default). Brute-force Protection
Brute-force Protection
Exponential lockout on repeated wrong attempts (FailedAttempt+PasswordLocked). Password Strength Validation
Password Strength Validation
Ensures users pick strong, non-trivial passwords. Event-Driven Design
Event-Driven Design
Easy to integrate into Kodular/AI2 blocks using simple success/error events. No Plaintext Storage
No Plaintext Storage
Only hashes + salts are stored — never the real password. Optional Hints
Optional Hints
Users can store non-sensitive hints to help them remember their password.
This extension is perfect for:
- Building apps that need a secure login system
- Protecting sensitive data inside your apps
- Creating personal password managers
- Any app where security and privacy matter
 How to Use
How to Use
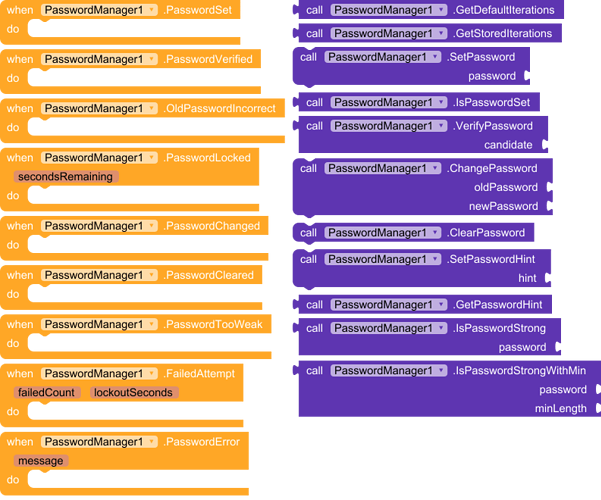
1. Setting a Master Password
PasswordManager1.SetPassword(TextBox1.Text)
- Fires PasswordSet if success.
- Fires PasswordTooWeak if the password is not strong enough.
2. Logging In
PasswordManager1.VerifyPassword(LoginBox.Text)
- Fires PasswordVerified if correct.
- Fires OldPasswordIncorrect if wrong.
- Fires FailedAttempt (with attempt count + lockout seconds).
- Fires PasswordLocked if user is locked out and must wait.
3. Changing Password
PasswordManager1.ChangePassword(OldBox.Text, NewBox.Text)
- Fires PasswordChanged if success.
- Fires OldPasswordIncorrect if old password is wrong.
- Fires PasswordTooWeak if new password is weak.
4. Reset / Clear Password
PasswordManager1.ClearPassword()
- Fires PasswordCleared after wiping stored password.
5. Optional Hint
PasswordManager1.SetPasswordHint("My childhood pet")
Label1.Text = PasswordManager1.GetPasswordHint()
 Events Cheat-Sheet
Events Cheat-Sheet
- PasswordSet → Fired after password created.
- PasswordTooWeak → Fired if password does not meet strength rules.
- PasswordVerified → Fired when login success.
- OldPasswordIncorrect → Fired when wrong password entered.
- PasswordChanged → Fired when password updated.
- PasswordCleared → Fired after reset.
- FailedAttempt(failedCount, lockoutSeconds) → Fired each wrong try.
- PasswordLocked(secondsRemaining) → Fired if user is still locked.
- PasswordError(message) → Fired if something unexpected goes wrong.
Password Strength Rules
Password must:
- Be at least 6 characters
- Include a digit (0–9)
- Include an uppercase letter (A–Z)
- Include a special character (!, @, #, etc.)
 Extension Details
Extension Details
- Extension Name:
PasswordManager - Version:
v1.0 - Created by:
Mahir Labib - Compatible with: Kodular, AI2, etc.
- Storage: One-way hashing, SharedPreferences (internal & secure)
- Size: Lightweight (< 100KB)
- Dependencies: None
- Built using: FAST v2.6.0
 Download
Download
com.mahir.passwordmanager.aix (11.8 KB)
 Example Use-Cases
Example Use-Cases
- A notes app where users must unlock their notes with a password.
- A gallery app to protect private photos.
- A password vault built inside Kodular.
- Any app where you want a secure login screen.
 Final Thoughts
Final Thoughts
The PasswordManager extension brings real-world security practices into Kodular & AI2 apps. By combining hashing, salting, key stretching, and brute-force lockout, it helps developers protect users against the most common threats.
![]() Build safer apps. Protect user trust. Use PasswordManager.
Build safer apps. Protect user trust. Use PasswordManager.
 Feedback Welcome!
Feedback Welcome!
If you like it, comment ![]()
If you want new features like fingerprint support, multi-user, or backup/restore, just request below!
#passwordmanager